Intel Overview
Chainara Intel is an active threat intelligence collection platform that deploys AI-powered personas to infiltrate crypto scam operations on Discord, Twitter/X, and other social platforms.
What it does
| Capability | Description |
|---|---|
| Personas | AI agents that pose as potential victims to engage scammers |
| Conversation monitoring | Real-time visibility into all active persona conversations |
| Threat extraction | Automatically extracts wallet addresses, phishing URLs, and domains from conversations |
| Domain monitoring | Tracks suspicious domains with automated periodic scanning |
| Forensic workers | Headless browsers that automatically investigate discovered URLs |
| Dark Web Hunter | Autonomous Tor-based agent that searches .onion sites and dark web markets for fraud infrastructure |
| Threat maps | Infrastructure discovery mapping domain/IP relationships |
| Intelligence reports | AI-generated forensic reports from automated investigations |
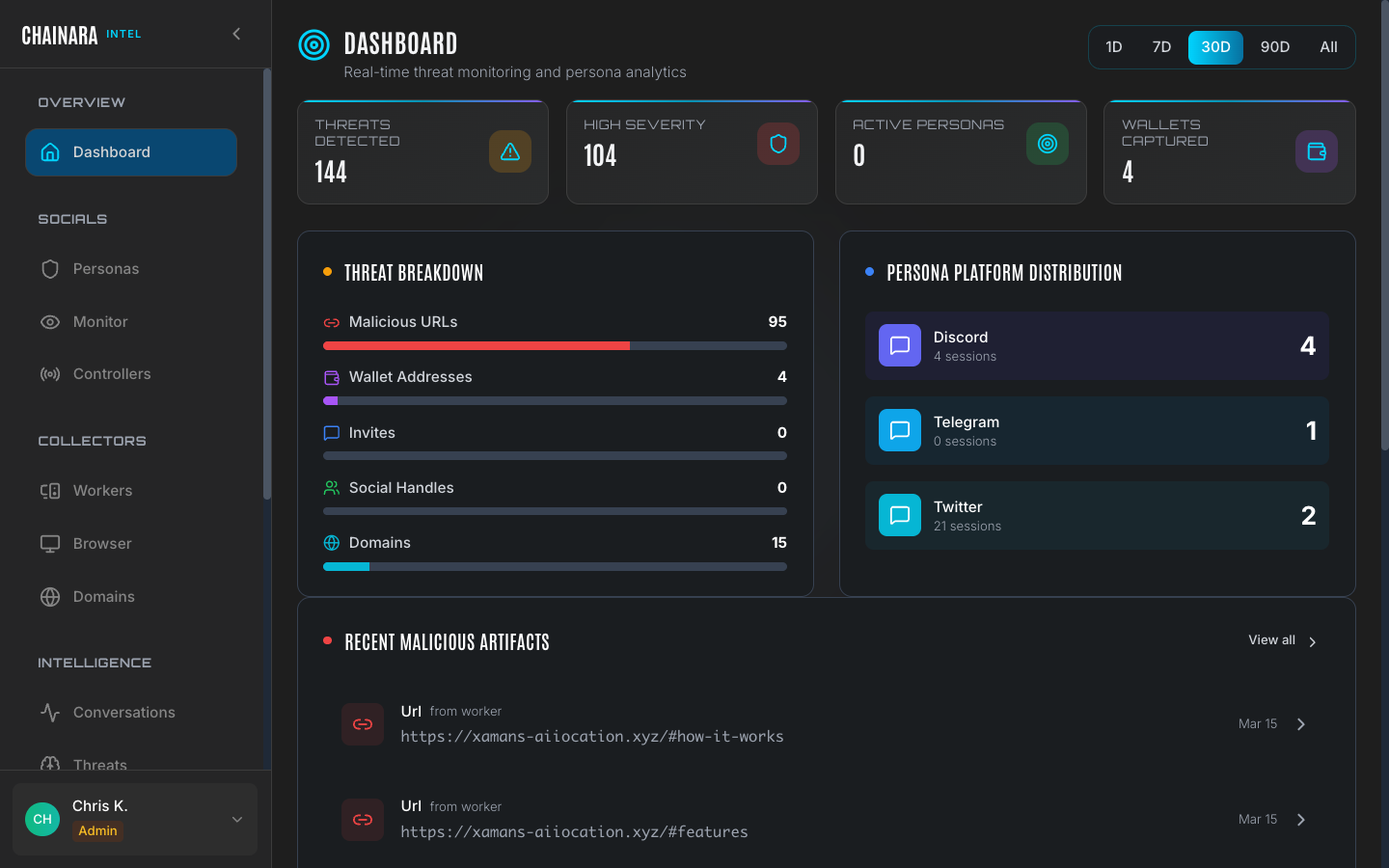
Dashboard stats
The dashboard shows live counts reflecting the current state of the system. Values update in real time as new threats are discovered, conversations occur, and workers complete investigations.
| Metric | Description |
|---|---|
| Threats detected | Total IOCs collected across all sources |
| High severity | Subset classified as High or Critical severity |
| Active personas | Personas currently deployed and engaging |
| Wallets captured | Unique crypto addresses extracted from conversations |
| URLs | Phishing/scam URLs discovered |
| Domains | Domains added to the monitoring list |
Platform distribution
Intel monitors scammer activity across social platforms including Discord, Twitter/X, and Telegram. The distribution of active conversations across these platforms is visible on the dashboard, giving you an at-a-glance view of where persona activity is concentrated.
How an Intel operation works
Understanding the end-to-end flow helps you use every section of the platform effectively:
Intel → Platform sync
Intel and Platform share the same backend threat database. When Intel extracts a wallet address or domain from a scammer conversation, it is submitted directly to the Platform backend: no manual export required. Within seconds:
- The wallet appears in Platform's wallet database with an initial risk score
- The domain is queued through the 8-stage Domain Engine pipeline
- Both appear in the Platform threat feed and are available via API
This means threat intelligence collected by personas today is available to your SIEM, exchange screening system, or compliance tool within minutes. There is no separate sync job to run or schedule: the write to Platform happens inline as each IOC is extracted.
Intel and Platform threat data are unified at the database level. Deleting or editing an IOC in Intel also affects its representation in Platform. Exercise caution when bulk-deleting artifacts.
Navigation
The Intel sidebar is organized into sections:
OVERVIEW
- Dashboard
SOCIALS
- Personas: persona agent profiles
- Monitor: real-time conversation view
- Controllers: Discord/Telegram server management
COLLECTORS
- Workers: automated investigation workers
- Dark Web Hunter: Tor-based dark web intelligence agent
- Browser: live browser session viewer
- Domains: domain monitoring
INTELLIGENCE
- Conversations: archived conversation sessions
- Threats: threat data and IOC feed
- Maps: infrastructure discovery maps
- Reports: AI-generated forensic reports
SETTINGS / ADMIN
- Settings: LLM, integrations, security config
- Artifacts: collected IOC artifact database
- Logs: system audit trail