Reports
The Reports page contains AI-generated forensic intelligence reports produced by worker investigations. Each report documents what a worker found when investigating a suspicious URL or domain: including the scam type, risk score, all extracted IOCs, visual evidence, and recommended actions.
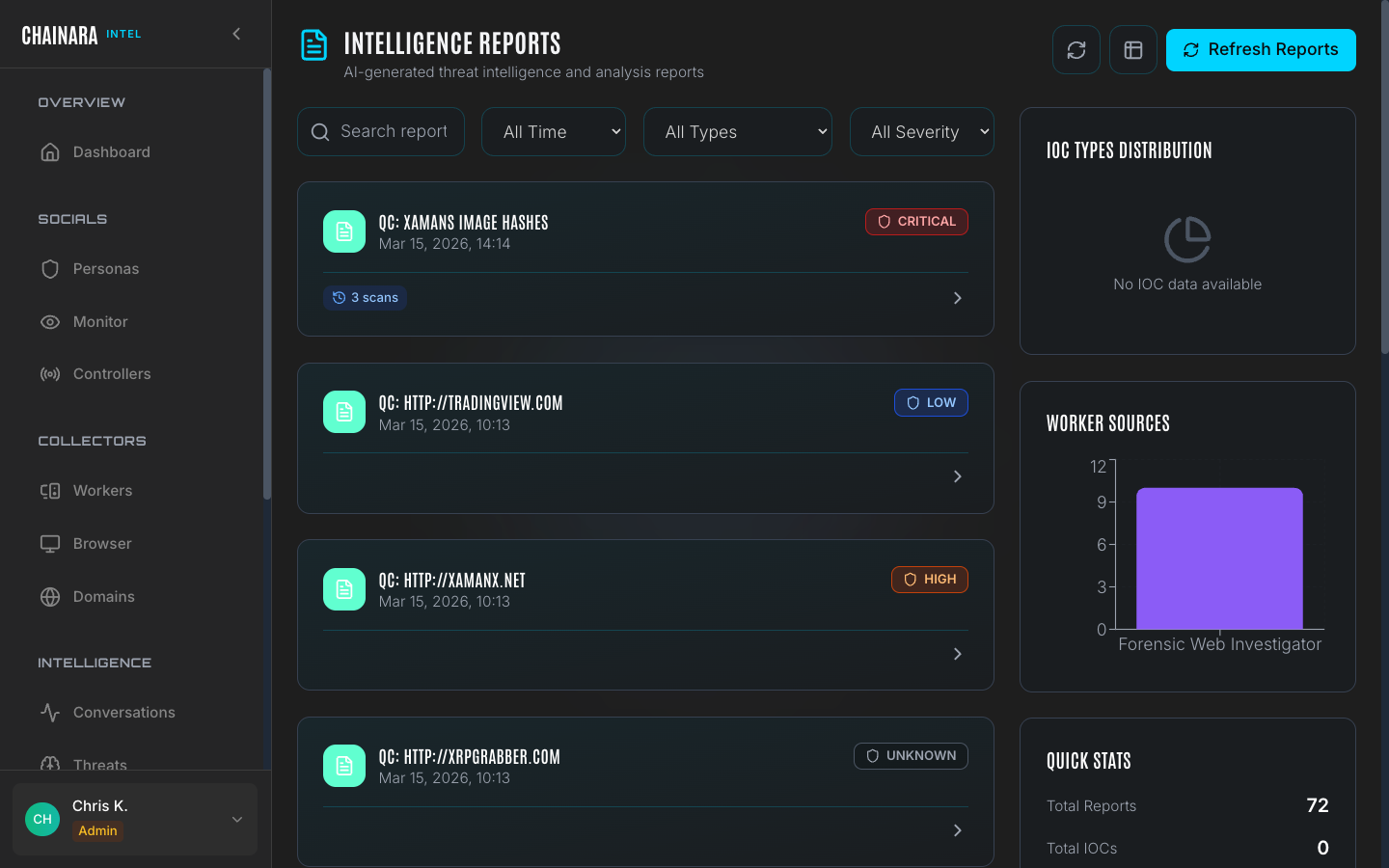
Report list
Reports accumulate as workers complete investigations. The list can be filtered to narrow down to the reports most relevant to your current focus:
| Filter | Options |
|---|---|
| Time range | All Time / Today / This Week / This Month |
| Type | Threat Reports / Session Analysis / Daily Summary |
| Severity | Critical / High / Medium / Low / Unknown |
Report severity examples
| Report type | Severity | Description |
|---|---|---|
| Worker navigation task | LOW / UNKNOWN | Automated site traversal with inconclusive threat findings |
| Phishing domain scan | HIGH | Known brand-impersonation site with credential harvest form |
| Investment scam site | CRITICAL | Crypto airdrop or giveaway scam with wallet harvest mechanism |
| Domain monitor alert | LOW–HIGH | Auto-generated report from a scheduled domain availability check |
Report detail
Click any report to open its full forensic detail view.
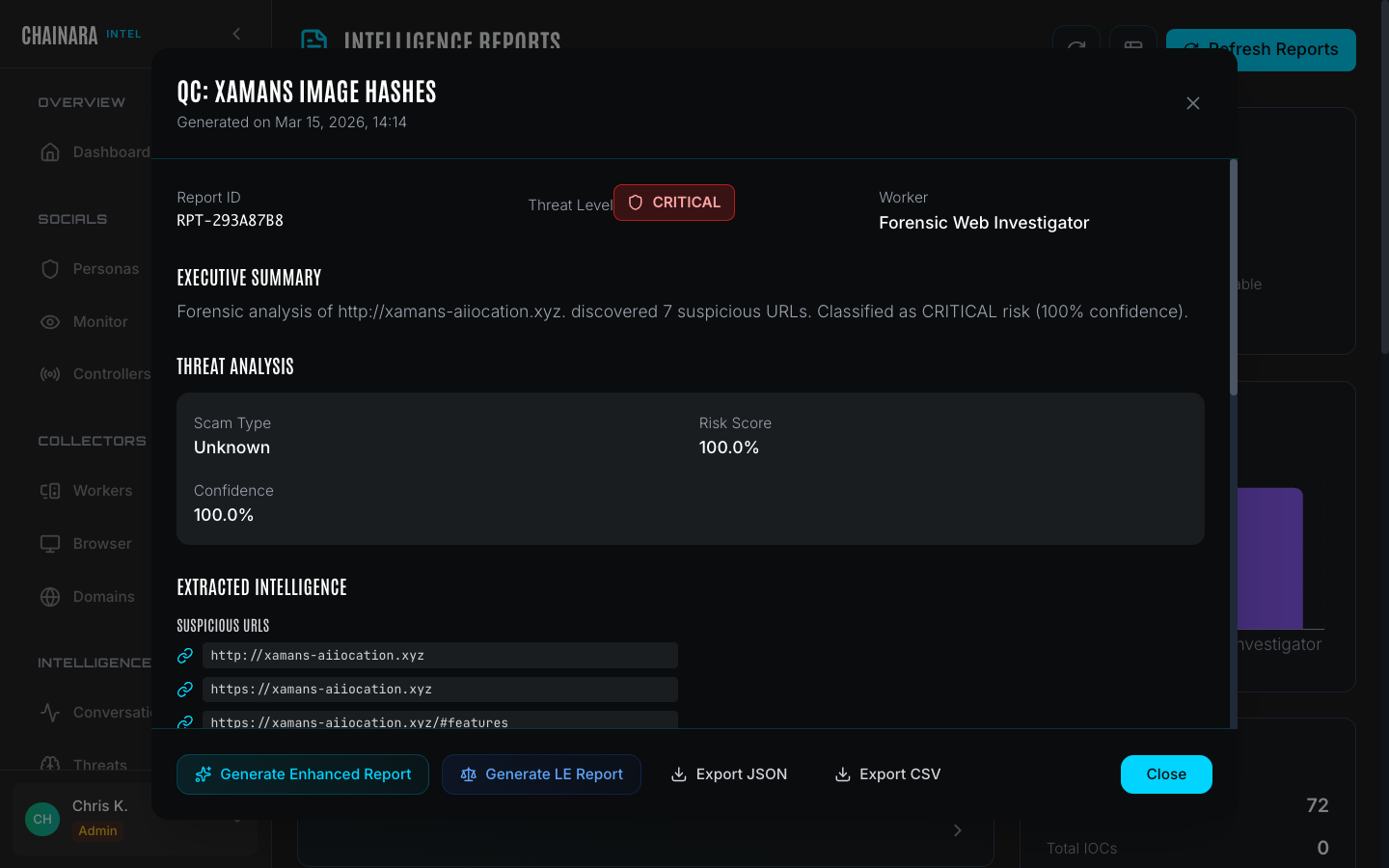
Header
The report header provides identifying metadata:
| Field | Description |
|---|---|
| Report ID | Unique identifier for this report (e.g. RPT-XXXXXXXX) |
| Threat level | CRITICAL / HIGH / MEDIUM / LOW / UNKNOWN |
| Worker | The automated worker that generated this report |
| Generated | Exact timestamp when the investigation completed |
| Target URL | The URL or domain that was investigated |
Executive summary
A one-paragraph AI-generated narrative summarizing the key findings: what type of scam the site runs, how many IOCs were discovered, and the overall risk classification with a confidence percentage. This section is written to be readable by non-technical stakeholders and is suitable for direct inclusion in incident reports or briefings.
Threat analysis
| Field | Description |
|---|---|
| Scam type | Categorical classification: Investment Scam, Phishing, Fake Exchange, Airdrop/Giveaway Fraud, Seed Phrase Harvest, etc. |
| Risk score | 0–100% likelihood the site is malicious, based on LLM analysis of all collected evidence |
| Confidence | The model's confidence in the scam type classification |
Extracted intelligence
A structured list of every IOC the worker discovered during the investigation:
| IOC type | Description |
|---|---|
| Suspicious URLs | Every URL encountered during the site crawl, including redirect chains and embedded links |
| Wallet addresses | Any crypto addresses found on the page, in scripts, or in form destinations |
| Forms detected | Input forms identified that may harvest credentials, seed phrases, or wallet keys: listed with URL and field names |
All extracted IOCs are automatically added to Artifacts and synced to the Threats database.
Evidence collected
Visual and technical evidence captured during the investigation:
- Screenshots: full-page captures taken at each navigation step, viewable inline within the report
- Form data: the URL and input field names of any detected harvest forms
- Network requests: third-party requests and loaded resources recorded during the session
- Redirect chain: the full sequence of redirects followed to reach the final page
Recommendations
Action items generated by the Threat Assessment LLM, calibrated to the threat level and the specific IOCs found. The LLM reviews all collected evidence: scam type, extracted wallets and domains, site content: and produces recommendations relevant to the specific threat rather than generic guidance.
| Threat level | Typical recommendations |
|---|---|
| CRITICAL | Block the domain immediately, flag associated wallets, file report with CISA or IC3, submit to hosting provider for takedown |
| HIGH | Monitor domain closely, flag wallets, submit to phishing databases (PhishTank, Google Safe Browsing) |
| MEDIUM | Continue monitoring, add to watchlist, re-scan in 48 hours |
| LOW / UNKNOWN | Archive for reference, flag if seen again |
Export options
Each report supports four export formats:
| Format | Use case |
|---|---|
| Enhanced report | Detailed AI-generated narrative in formatted PDF: suitable for executive briefings |
| LE report | Law enforcement formatted report with evidence chain documentation and legal language |
| JSON | Raw structured report data for ingestion into SIEM, ticketing, or analysis platforms |
| CSV | Tabular export of extracted IOCs for spreadsheet analysis |
Report retention
Reports are retained indefinitely. There is no automatic archival or expiry. Use the time range filter to limit the list to recent reports when the volume becomes large.
Worker sources chart
The right panel on the Reports list page shows a bar chart of report volume by worker. Use this to identify which workers are most active and where the bulk of intelligence is coming from: a sudden drop in reports from a specific worker may indicate it has stalled or needs attention.