Fraud Intelligence
The Fraud Intelligence section aggregates all submitted fraud reports and known threat data into a centralized feed for the team.
Tabs
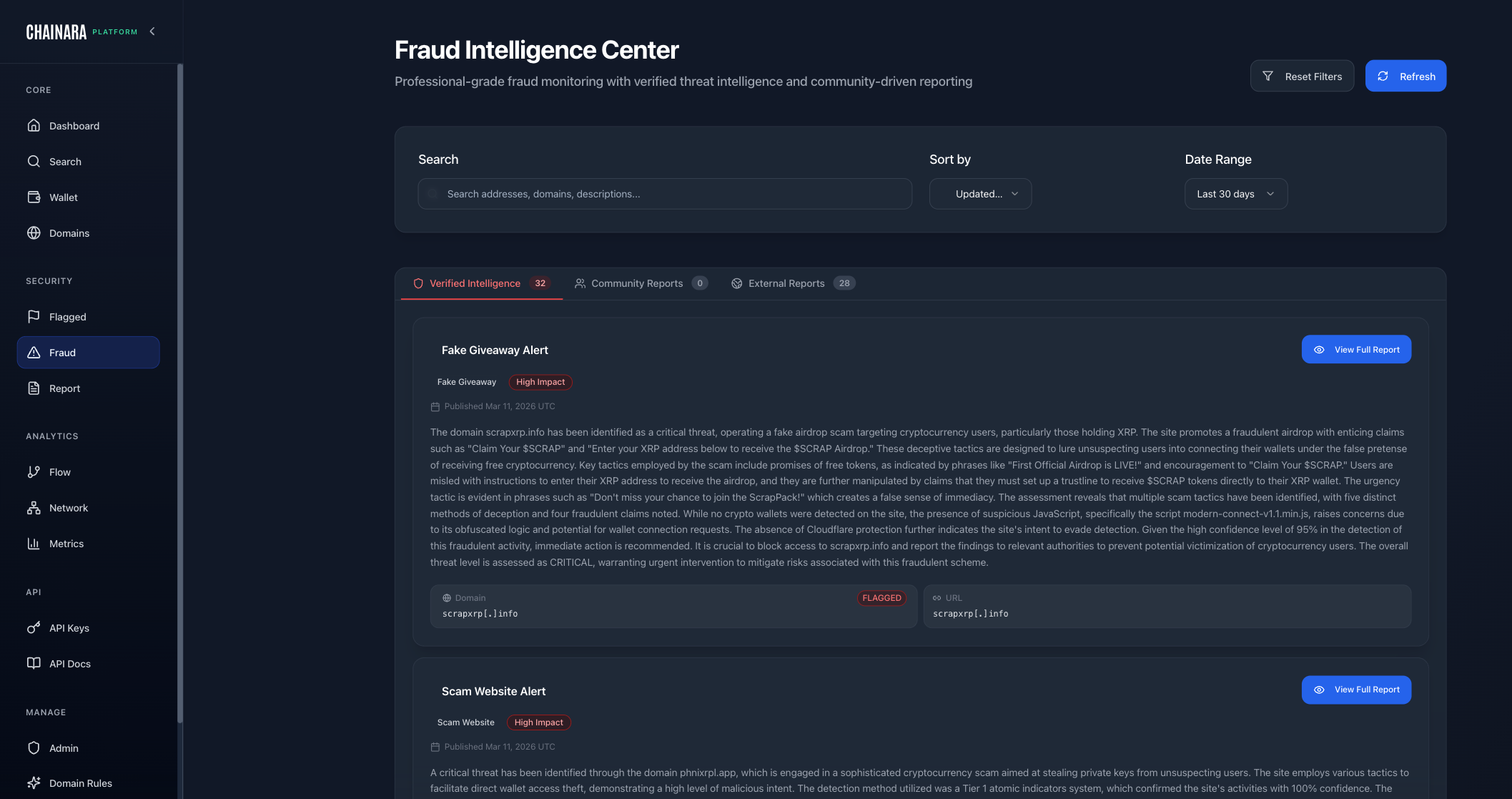
The Fraud Intelligence Center is split into tabs so you can focus on one source of intelligence at a time without losing context on the others:
| Tab | Source | Verification |
|---|---|---|
| Verified Intelligence | Internal fraud reports that have been reviewed and verified | Confirmed |
| Community Reports | Victim-submitted reports from across the platform | Pending until reviewed |
| External Reports (Enterprise) | Imported feeds (ChainAbuse, BitcoinAbuse, and other partner sources) | Source-attributed, surfaced for analyst review |
Community Reports also appear on the main dashboard once approved, so analysts see fresh community-sourced intelligence without needing to drill into Fraud Intelligence specifically.
What's in the Feed
The fraud intelligence feed shows:
- User-submitted fraud reports from the Report form
- Automatically detected fraud patterns from the domain engine and wallet scoring
- Imported threat data from partner feeds and external sources (visible to enterprise tenants in the External Reports tab)
- Ad-platform findings: crypto scams detected by the Ad Platform Scanners running against Meta, Bing, Google, and LinkedIn
- Each entry includes: wallet address, domain, scam type, evidence, and submitter
Report Details
Click any entry to expand the full report:
| Field | Description |
|---|---|
| Report ID | Unique identifier for the report |
| Wallet Address | The XRP address involved |
| Domain | Associated phishing/scam domain if any |
| Scam Type | See categories below |
| Description | Freeform notes from the reporter |
| Evidence | Attached screenshots, transaction IDs, links |
| Status | Pending / Verified / Dismissed |
| Submitted By | User or system that submitted the report |
| Submitted At | Timestamp |
Fraud Categories
Reports are classified into these categories. For a detailed breakdown of each category including detection methodology, see Threat Categories.
| Category | Description |
|---|---|
| Scam | General deception to steal XRP |
| Phishing | Fake websites/messages mimicking legitimate services |
| Fake Giveaway | "Send X XRP, get 2X back" schemes |
| Rug Pull | Project abandonment after collecting funds |
| Money Laundering | Layering/washing stolen crypto through many wallets |
| Ponzi / HYIP | High-yield investment promises with no real returns |
| Exchange Hack | Stolen funds traced from exchange breaches |
| Mixer / Tumbler | Privacy services used to obscure illicit fund origin |
Verification Workflow
Reports go through a verification pipeline:
Pending → In Review → Verified / Rejected / Disputed
- Pending: newly submitted, awaiting review
- In Review: an analyst or AI agent is evaluating
- Verified: confirmed as a real threat; wallet risk score updated
- Rejected: insufficient evidence or false positive
- Disputed: conflicting signals; needs additional review
Filtering and Search
Use the filters to narrow the feed:
- By scam type: filter to specific fraud categories
- By date range: focus on recent activity
- By status: view only unreviewed or verified reports
- By submitter: see reports from a specific user or system
Exporting Intelligence
Intelligence data can be exported via:
- CSV export from the UI
- API endpoint:
GET /api/v2/fraud-reports - Webhook: push new reports to your SIEM as they arrive (configure in Admin → Webhooks)